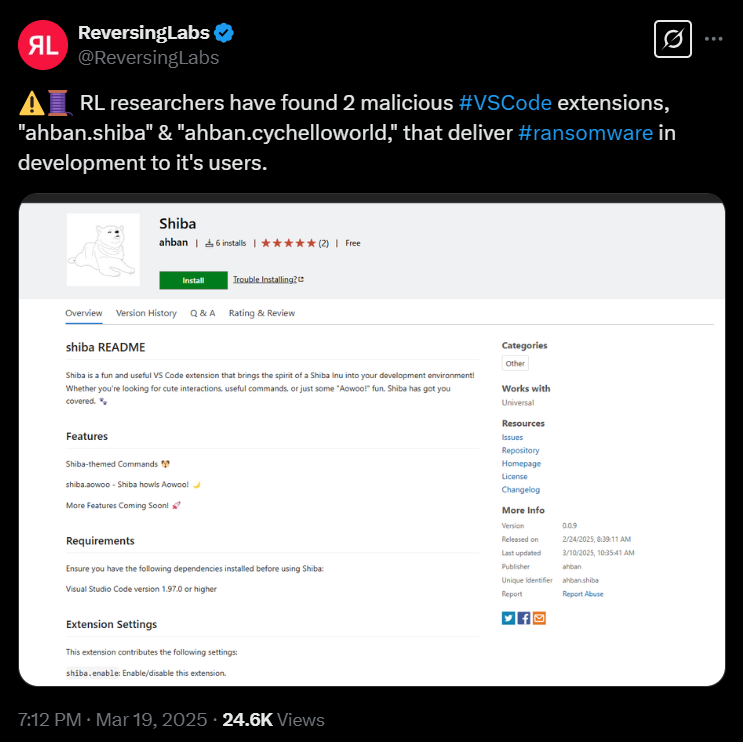
Researchers discover two malicious VSCode extensions (in the Visual Studio Code (VSCode) Marketplace) designed to deploy in-development ransomware.
Following discovery, the extensions "ahban.shiba" (uploaded on February 17, 2025) and "ahban.cychelloworld" (uploaded on October 27, 2024) have been removed from the VSCode Marketplace.
Both extensions, as identified by ReversingLabs, execute a PowerShell command that downloads and runs a script payload from a (command-and-control) C2 server.
The ransomware is believed to be in its developmental phase, encrypting files exclusively in a folder named "testShiba" on the victim’s Windows desktop (C:\users\%username%\Desktop\testShiba) and does not touch any other files.
Once the files are encrypted, the PowerShell payload displays a message, stating "Your files have been encrypted. Pay 1 ShibaCoin to ShibaWallet to recover them."
With no payment details or instructions provided, the malware appears to be an unfinished project by the threat actors.