A cyberattack that reportedly forced tens of thousands of systems offline at medical technology company Stryker this week has underscored a critical lesson for organisations worldwide. The incident highlights how essential it is for businesses to maintain robust, well-tested business continuity and disaster recovery plans capable of responding effectively to large-scale cyber disruptions.
The cyber campaign was attributed by the threat actor collective Handala, which issued statements claiming the attack was carried out in response to regional political developments. The group specifically referenced a recent airstrike on a school in Iran that reportedly killed over 160 children and also alleged that the victim organisation maintained connections with Israel. This pattern of politically framed targeting reflects the growing role of cyber operations as a tool for symbolic retaliation and narrative amplification in geopolitical disputes.
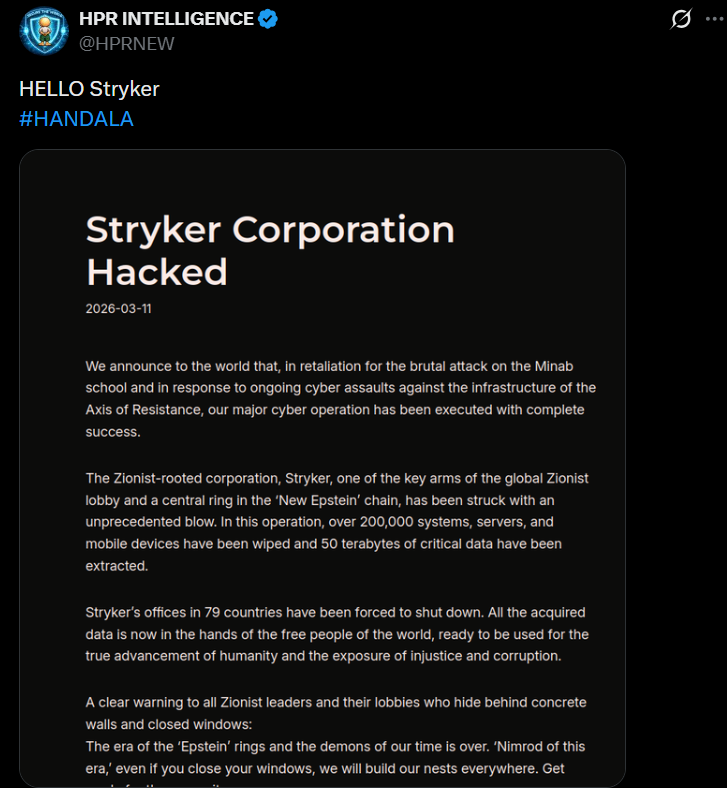 The group Handala said in a post on X that the attack resulted in the wiping of nearly 200,000 systems, including servers and mobile devices associated with Stryker’s infrastructure. The threat actors further claimed to have extracted roughly 50TB of company data as part of the operation. "Stryker's office in 79 countries have been forced to shut down," the group claimed. "All the acquired data is now in the hands of the free people of the world, ready to be used for the true advancement of humanity."
The group Handala said in a post on X that the attack resulted in the wiping of nearly 200,000 systems, including servers and mobile devices associated with Stryker’s infrastructure. The threat actors further claimed to have extracted roughly 50TB of company data as part of the operation. "Stryker's office in 79 countries have been forced to shut down," the group claimed. "All the acquired data is now in the hands of the free people of the world, ready to be used for the true advancement of humanity."
In a public update on Wednesday, Stryker Corporation characterised the incident as a global disruption impacting its Microsoft environment. The company indicated that the issue appears to have been contained, while investigations remain ongoing to determine the true extent of the compromise. It also noted that business continuity plans have been activated to ensure continued service for customers and partners. "We are committed to transparency and will keep stakeholders informed as we know more."
In a subsequent update issued Thursday, Stryker Corporation indicated that system restoration activities were ongoing as teams worked to recover impacted infrastructure. At the same time, the company reassured users that several key medical solutions, such as its robot-assisted surgical platform, healthcare professional communication platform, and advanced life-support monitoring and defibrillation devices, were unaffected and safe to operate.
A Critical Warning Sign
Cybersecurity experts have cautioned that Iranian-aligned threat groups may conduct retaliatory cyberattacks against US companies and critical cyber assets following military operations launched by the United States and Israel against Iran around two weeks ago. The wiper-style attack affecting Stryker Corporation is considered the first significant incident in this wave, though analysts expect further activity. Threat intelligence firm Flashpoint has noted that Iran’s Islamic Revolutionary Guard Corps has previously issued threats against several technology companies, including Amazon, Google, Microsoft, Oracle, Palantir Technologies and Nvidia.
The incident involving Stryker Corporation underscores a structural weakness in many business continuity frameworks — the reliance on the same digital environment for both operations and recovery. Kim Larsen, group CISO at Keepit, noted that when critical layers such as identity management systems, endpoints and backup infrastructure fail simultaneously during an attack, organisations may discover that their resilience strategies offer limited real-world protection.
Kim Larsen notes that multinational enterprises frequently struggle with business continuity and disaster recovery due to the distributed nature of their data ecosystems. With information spread across different platforms, regions and regulatory frameworks, organisations must navigate additional layers of complexity during a crisis — a factor that can delay recovery processes when speed and coordination are essential. “We also see sovereignty become a real constraint during recovery. If organizations don't have clear control over where their data lives and who governs access, legal and operational uncertainty can delay restoration when every hour counts," Larsen notes.

